Malware analysis Malicious activity
Por um escritor misterioso
Last updated 20 junho 2024

Feature Extraction and Detection of Malwares Using Machine Learning

How to build a malware analysis sandbox with Elastic Security

Malware Analysis Benefits Incident Response
Interactive Online Malware Sandbox

Cybersecurity Search Engine

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Interactive Online Malware Sandbox

Complex 'NKAbuse' Malware Uses Blockchain to Hide on Linux, IoT Machines

Malware Analysis: Protecting Your Network from Cyber Attacks

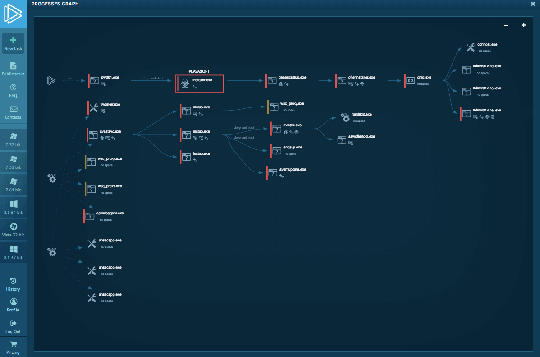
How to Analyze Malware's Network Traffic in A Sandbox
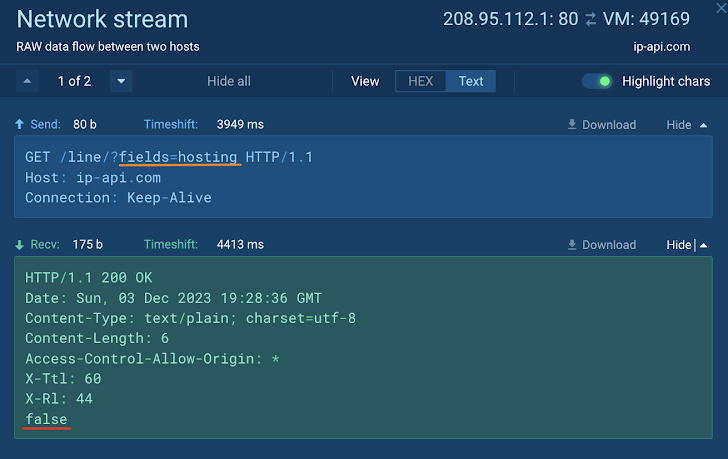
How to Analyze Malware's Network Traffic in A Sandbox

StopRansomware: Rhysida Ransomware

Malware analysis file Malicious activity

Dynamic malware analysis [34]
Recomendado para você
-
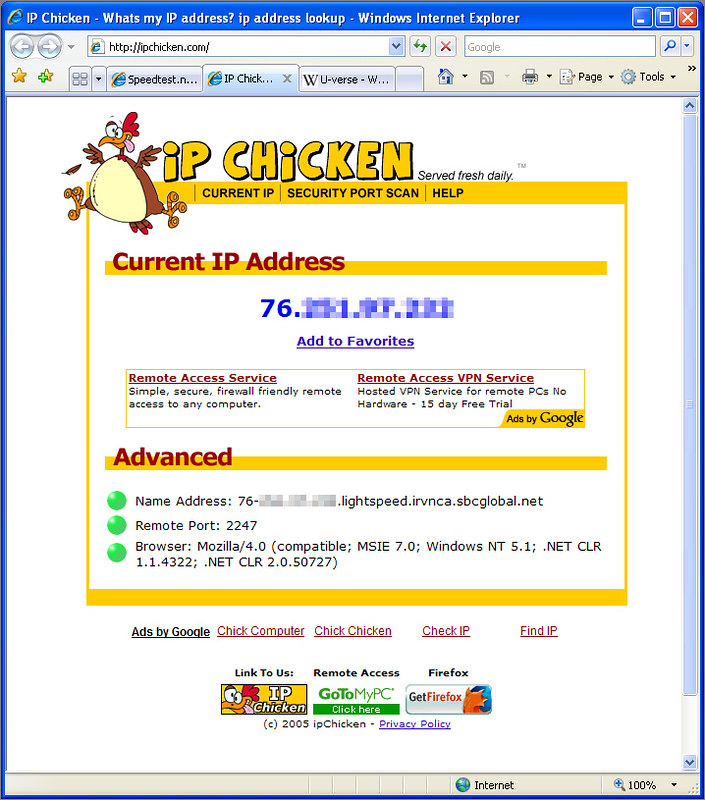 IPChicken, Woo hoo! Lightspeed!, Richard De Guzman20 junho 2024
IPChicken, Woo hoo! Lightspeed!, Richard De Guzman20 junho 2024 -
ipchicken|TikTok Search20 junho 2024
-
 IP Chicken - Served Fresh Daily20 junho 2024
IP Chicken - Served Fresh Daily20 junho 2024 -
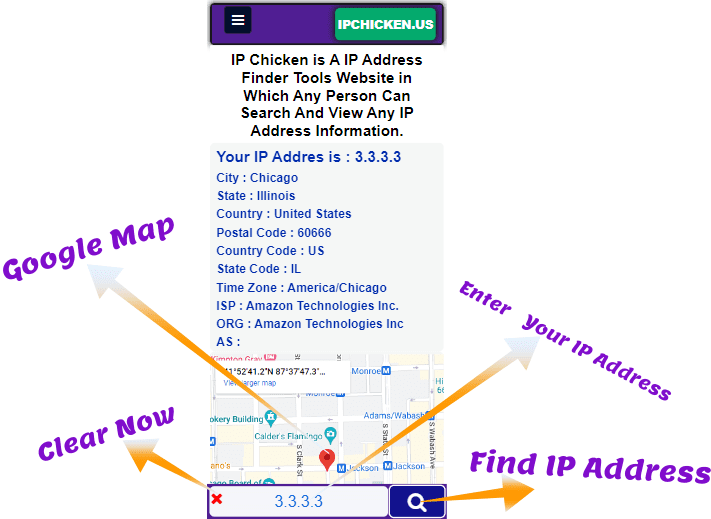 IP Chicken - What Is My IP Address See Your IP Address Free20 junho 2024
IP Chicken - What Is My IP Address See Your IP Address Free20 junho 2024 -
 shell - SSH socks proxy via jumphost - Stack Overflow20 junho 2024
shell - SSH socks proxy via jumphost - Stack Overflow20 junho 2024 -
 Top 74 Similar websites like ipchicken.com and alternatives20 junho 2024
Top 74 Similar websites like ipchicken.com and alternatives20 junho 2024 -
:max_bytes(150000):strip_icc()/D2-FindYourIPAddressinWindows-annotated-b0679c3607194bebafcba69fdf78982d.jpg) How to Find Your IP Address in Windows20 junho 2024
How to Find Your IP Address in Windows20 junho 2024 -
:max_bytes(150000):strip_icc()/SL_SEO_112119_AM_IPChickenWings_397-2000-ea1992c08520411c90e113fb5f6cdc0f.jpg) Instant Pot Chicken Wings Recipe20 junho 2024
Instant Pot Chicken Wings Recipe20 junho 2024 -
 Instant Pot Chicken Thighs20 junho 2024
Instant Pot Chicken Thighs20 junho 2024 -
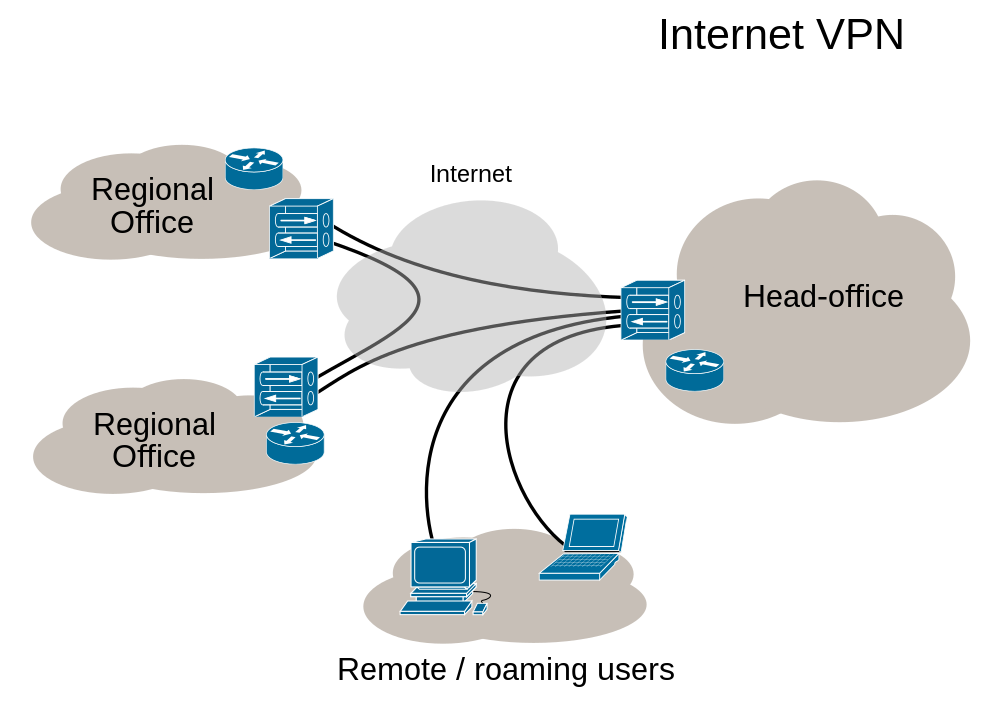 Newbie Question - OpenVPN Support Forum20 junho 2024
Newbie Question - OpenVPN Support Forum20 junho 2024
você pode gostar
-
 Sonic coloring page Free Printable Coloring Pages20 junho 2024
Sonic coloring page Free Printable Coloring Pages20 junho 2024 -
 Cantor Luiz Caldas toca no Clube do Choro nesta quinta-feira (8/9)20 junho 2024
Cantor Luiz Caldas toca no Clube do Choro nesta quinta-feira (8/9)20 junho 2024 -
 6 dicas de animes de guerra para você conhecer! - Estratégia Militares20 junho 2024
6 dicas de animes de guerra para você conhecer! - Estratégia Militares20 junho 2024 -
 Boneca para maquiar no Ibis Paint Painting, Mini drawings, Comic art20 junho 2024
Boneca para maquiar no Ibis Paint Painting, Mini drawings, Comic art20 junho 2024 -
 Andrea Botez trains to become a boxer.20 junho 2024
Andrea Botez trains to become a boxer.20 junho 2024 -
 Lovisa shares glitter as profit growth shines20 junho 2024
Lovisa shares glitter as profit growth shines20 junho 2024 -
 Best Aesthetic Christmas Wallpapers Backgrounds20 junho 2024
Best Aesthetic Christmas Wallpapers Backgrounds20 junho 2024 -
 Best keyboard and mouse combo for gaming under ₹3,000 in India20 junho 2024
Best keyboard and mouse combo for gaming under ₹3,000 in India20 junho 2024 -
como desenhar o yoriichi|Pesquisa do TikTok20 junho 2024
-
 Roblox Shindo Life Private Server Codes List (December 2023) - Pro20 junho 2024
Roblox Shindo Life Private Server Codes List (December 2023) - Pro20 junho 2024

