SQL injection and XSS: what white hat hackers know about trusting
Por um escritor misterioso
Last updated 20 junho 2024

Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be

What Is Hacking? - White Hat, Black Hat, Gray Hat Hackers
sql injection, Breaking Cybersecurity News

Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques

Ethical Hacking by Nancy Idiong, PDF, Security Hacker

SQL Injection Prevention and Mitigation – The Cybersecurity Man
What are the most common security attacks to PHP web applications? - Quora

40+ Best Cross-Site Scripting (XSS) Courses and Certifications for 2023

sql injection, Breaking Cybersecurity News

7 Ways To Earn Money as an Ethical Hacker - GeeksforGeeks

Tool Release: Magisk Module – Conscrypt Trust User Certs, NCC Group Research Blog
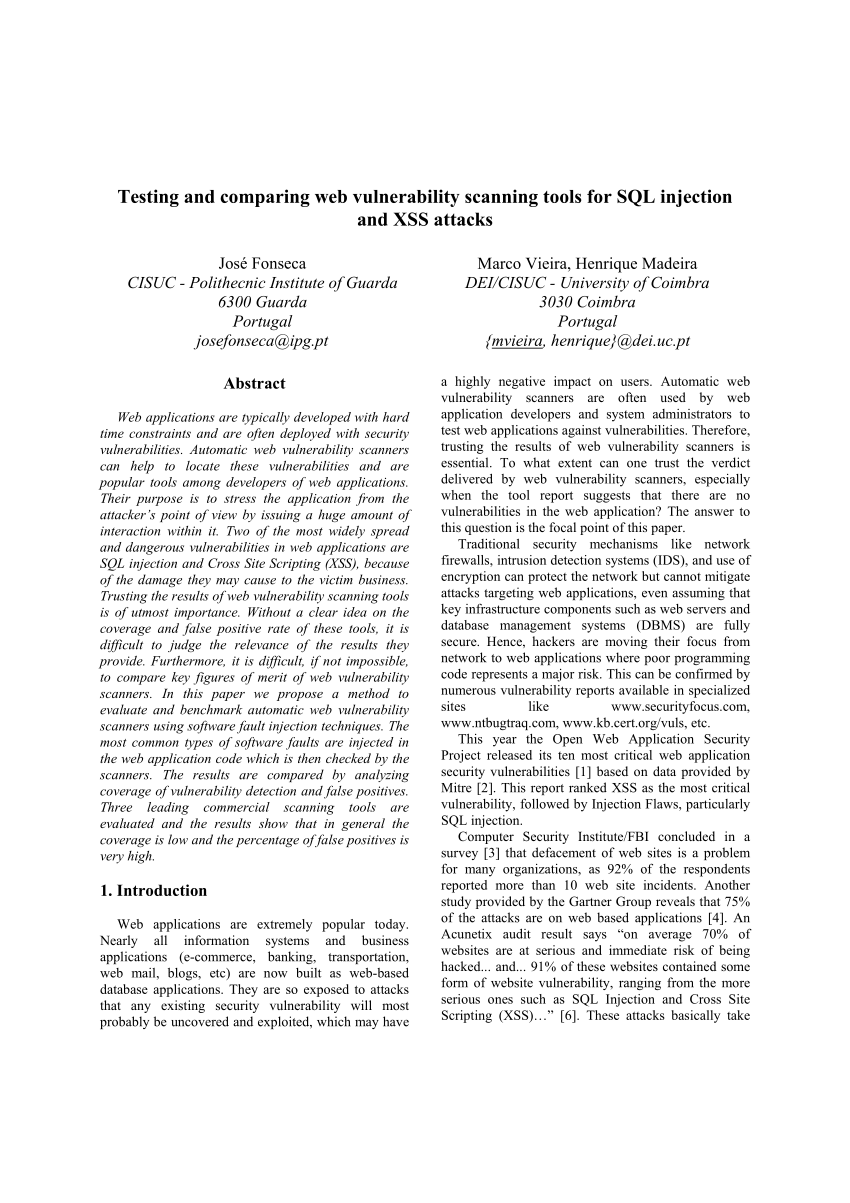
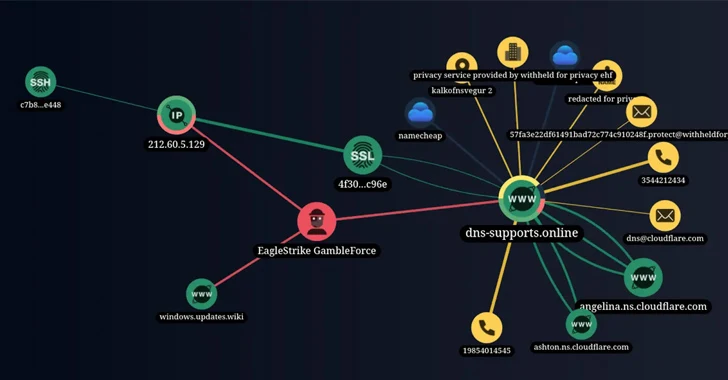
PDF) Testing and Comparing Web Vulnerability Scanning Tools for SQL Injection and XSS Attacks
Hacking and Your Cybersecurity Future

Blind SQL Injection at fasteditor.hema.com, by Jonathan Bouman

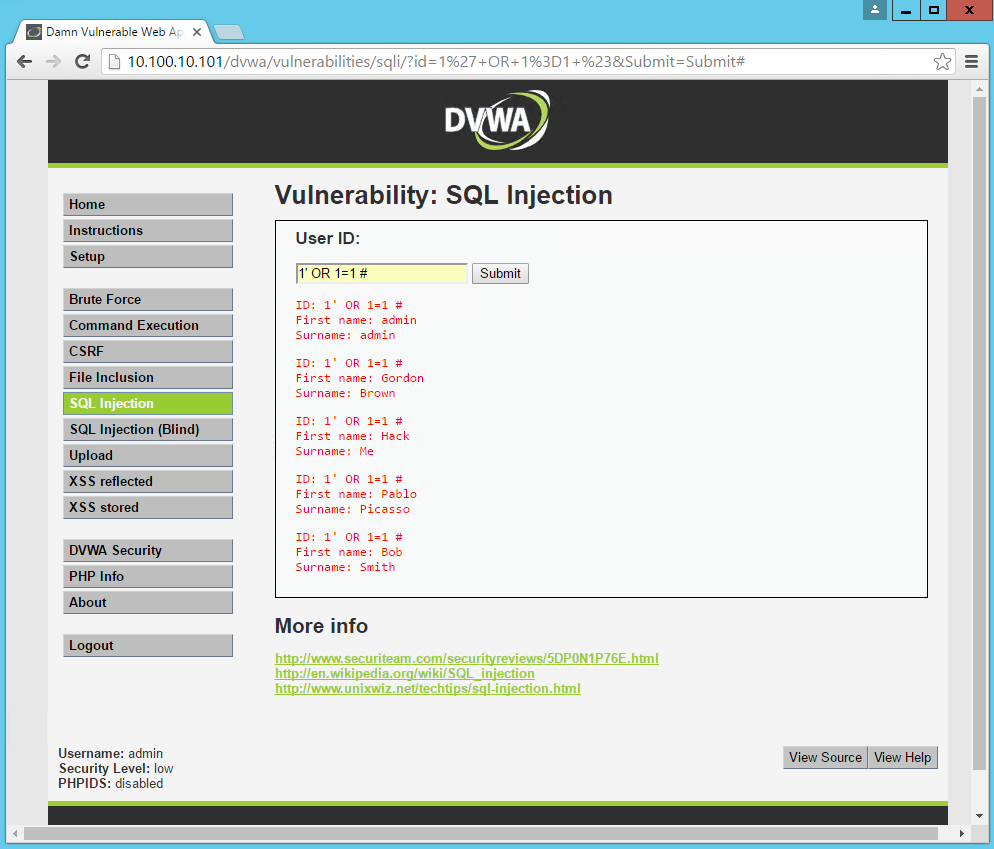
What is SQL Injection?, Explanation & Protection
Recomendado para você
-
 Cross Site Scripting (XSS) - Payload Generator20 junho 2024
Cross Site Scripting (XSS) - Payload Generator20 junho 2024 -
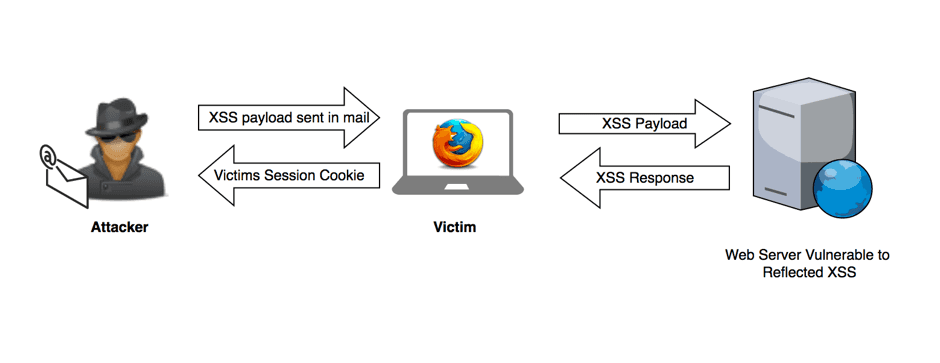 What is Cross-site Scripting (XSS)? Stored, DOM & Reflected Examples20 junho 2024
What is Cross-site Scripting (XSS)? Stored, DOM & Reflected Examples20 junho 2024 -
 Why Injection still matters, XSS attacks20 junho 2024
Why Injection still matters, XSS attacks20 junho 2024 -
 How to craft an XSS payload to create an admin user in Wordpress20 junho 2024
How to craft an XSS payload to create an admin user in Wordpress20 junho 2024 -
 Reflected XSS, How to Prevent a Non-Persistent Attack20 junho 2024
Reflected XSS, How to Prevent a Non-Persistent Attack20 junho 2024 -
 Cross-Site Scripting: XSS Injection » Hacking Lethani20 junho 2024
Cross-Site Scripting: XSS Injection » Hacking Lethani20 junho 2024 -
 DOM Based XSS Attack Tutorial - How it works?20 junho 2024
DOM Based XSS Attack Tutorial - How it works?20 junho 2024 -
 Understanding Cross-Site Scripting Attacks20 junho 2024
Understanding Cross-Site Scripting Attacks20 junho 2024 -
 Lab - XSS and CORS João Paulo Barraca20 junho 2024
Lab - XSS and CORS João Paulo Barraca20 junho 2024 -
 Vulnérabilité XSS, ou injection de code indirecte à distance20 junho 2024
Vulnérabilité XSS, ou injection de code indirecte à distance20 junho 2024
você pode gostar
-
 Você conhece o aplicativo da NSports?20 junho 2024
Você conhece o aplicativo da NSports?20 junho 2024 -
:strip_icc()/Photo-Nov-16-1-22-37-PM-d39ebc9b4ec1408ebcbb3fcf9b655120.jpeg) 11 Friendsgiving Decorating Ideas for a Chic Soirée20 junho 2024
11 Friendsgiving Decorating Ideas for a Chic Soirée20 junho 2024 -
 Jogo Barbie Princess Puzzle no Jogos 36020 junho 2024
Jogo Barbie Princess Puzzle no Jogos 36020 junho 2024 -
 Jenny Wakeman by Michael4300 on DeviantArt20 junho 2024
Jenny Wakeman by Michael4300 on DeviantArt20 junho 2024 -
 A crescente ameaça ao poder de Mark Zuckerberg, dono do Facebook20 junho 2024
A crescente ameaça ao poder de Mark Zuckerberg, dono do Facebook20 junho 2024 -
TheFilme20 junho 2024
-
 KING LEGACY Script Pastebin 2023 UPDATE 4.6 AUTO FARM20 junho 2024
KING LEGACY Script Pastebin 2023 UPDATE 4.6 AUTO FARM20 junho 2024 -
 Shingeki no Kyojin: The Final Season - Kanketsu-hen - 01 - Lost in Anime20 junho 2024
Shingeki no Kyojin: The Final Season - Kanketsu-hen - 01 - Lost in Anime20 junho 2024 -
 MACACAO PIJAMA KIGURUMI VERAO SONIC INFANTIL 8 A 10 ANOS – Loja20 junho 2024
MACACAO PIJAMA KIGURUMI VERAO SONIC INFANTIL 8 A 10 ANOS – Loja20 junho 2024 -
 Assistir Mamahaha no Tsurego ga Motokano datta - Episódio 001 Online em HD - AnimesROLL20 junho 2024
Assistir Mamahaha no Tsurego ga Motokano datta - Episódio 001 Online em HD - AnimesROLL20 junho 2024
