Pawn Storm Abuses OAuth In Social Engineering Attacks
Por um escritor misterioso
Last updated 08 junho 2024
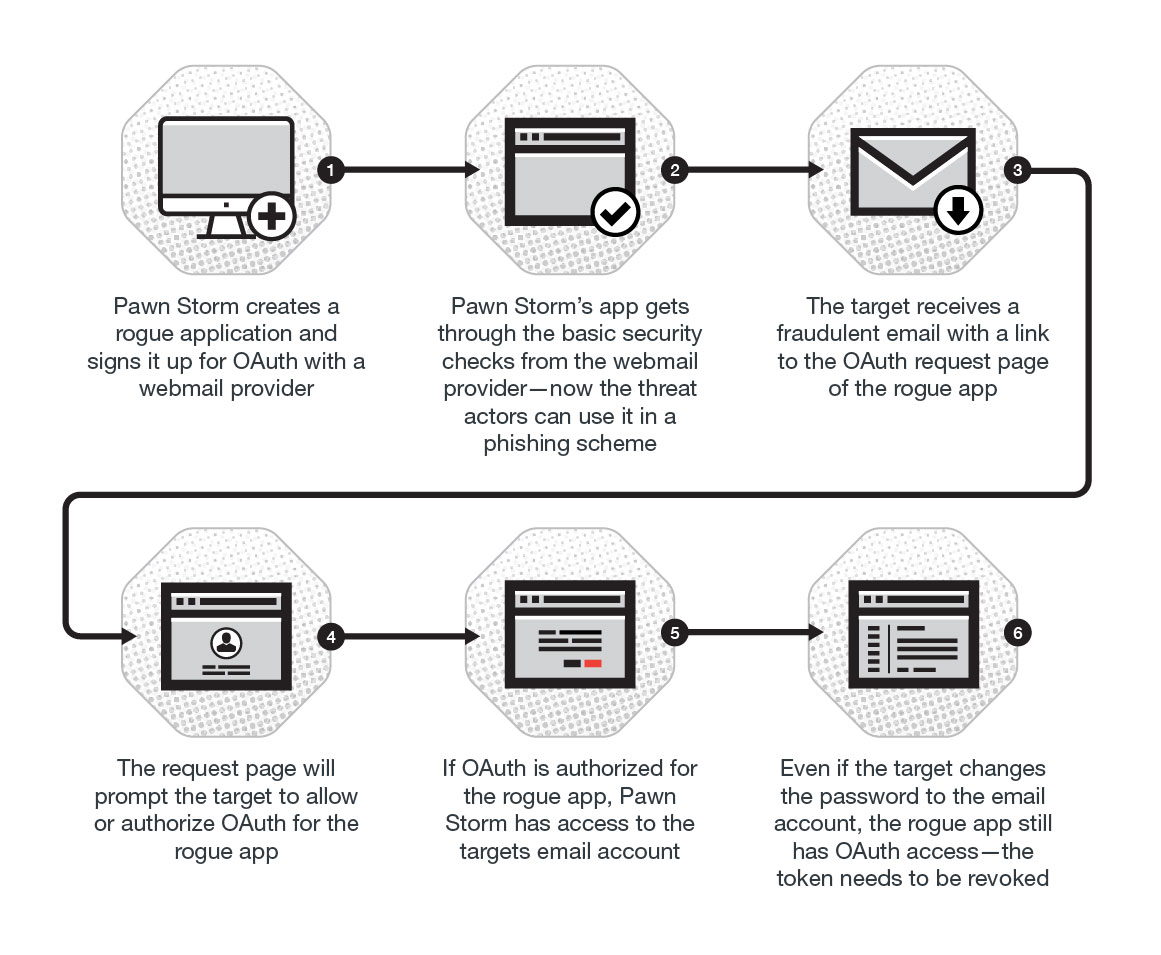
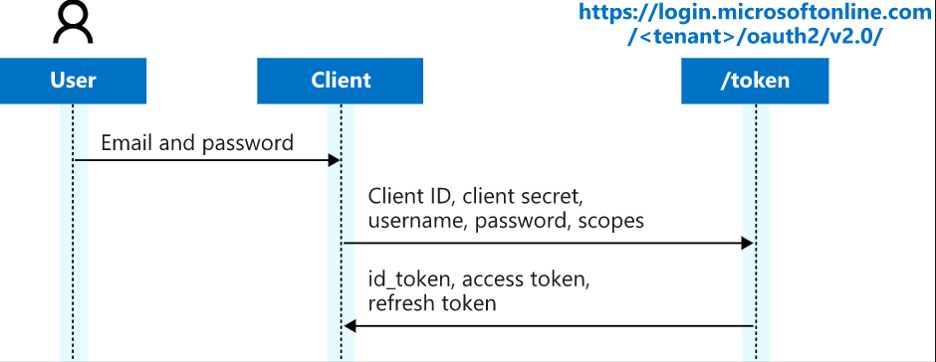
This blog post discusses how Pawn Storm abused Open Authentication (OAuth) in advanced social engineering schemes. High profile users of free webmail were targeted by campaigns between 2015 and 2016.

OAuth, Breaking Cybersecurity News
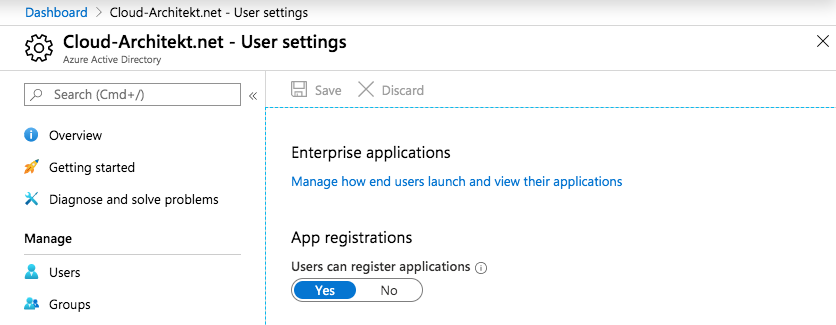
Detection and Mitigation of Illicit Consent Grant Attacks in Azure AD - Thomas Naunheim
Fake Honeypots: A Defensive Tactic for Cyberspace
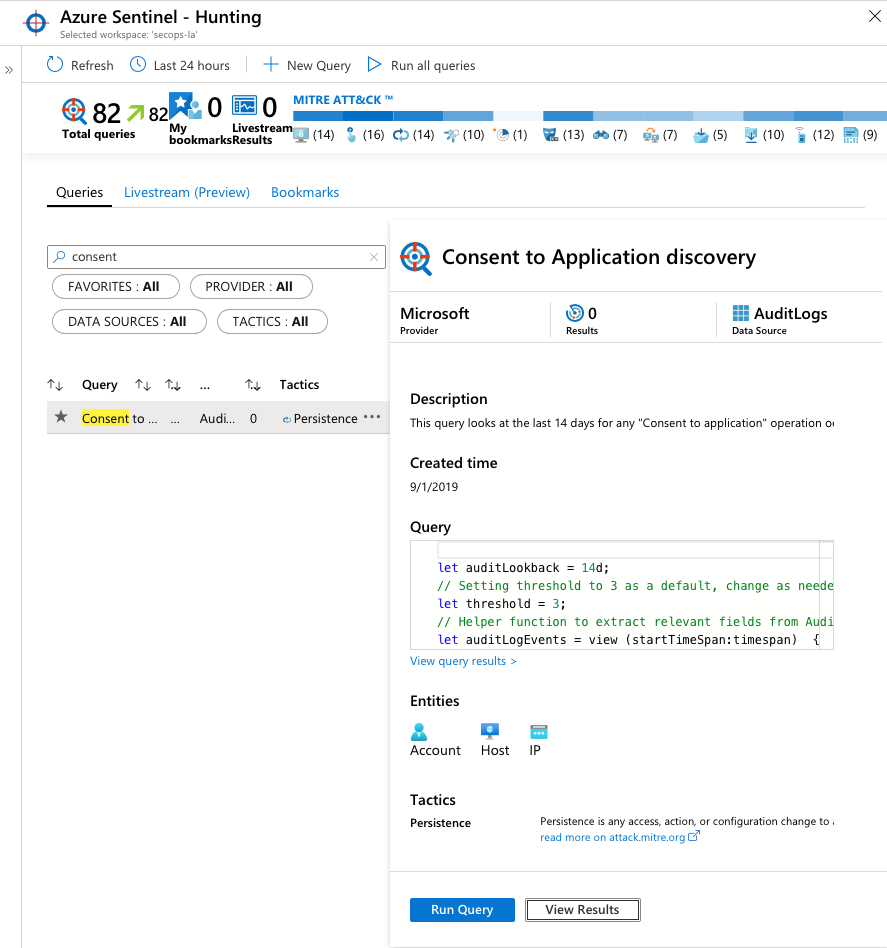
Detection and Mitigation of Illicit Consent Grant Attacks in Azure AD - Thomas Naunheim

APT28 relies on PowerPoint Mouseover to deliver Graphite malware
TrustedSec Practical OAuth Abuse for Offensive Operations – Part 1
Pawn Storm's Lack of Sophistication as a Strategy

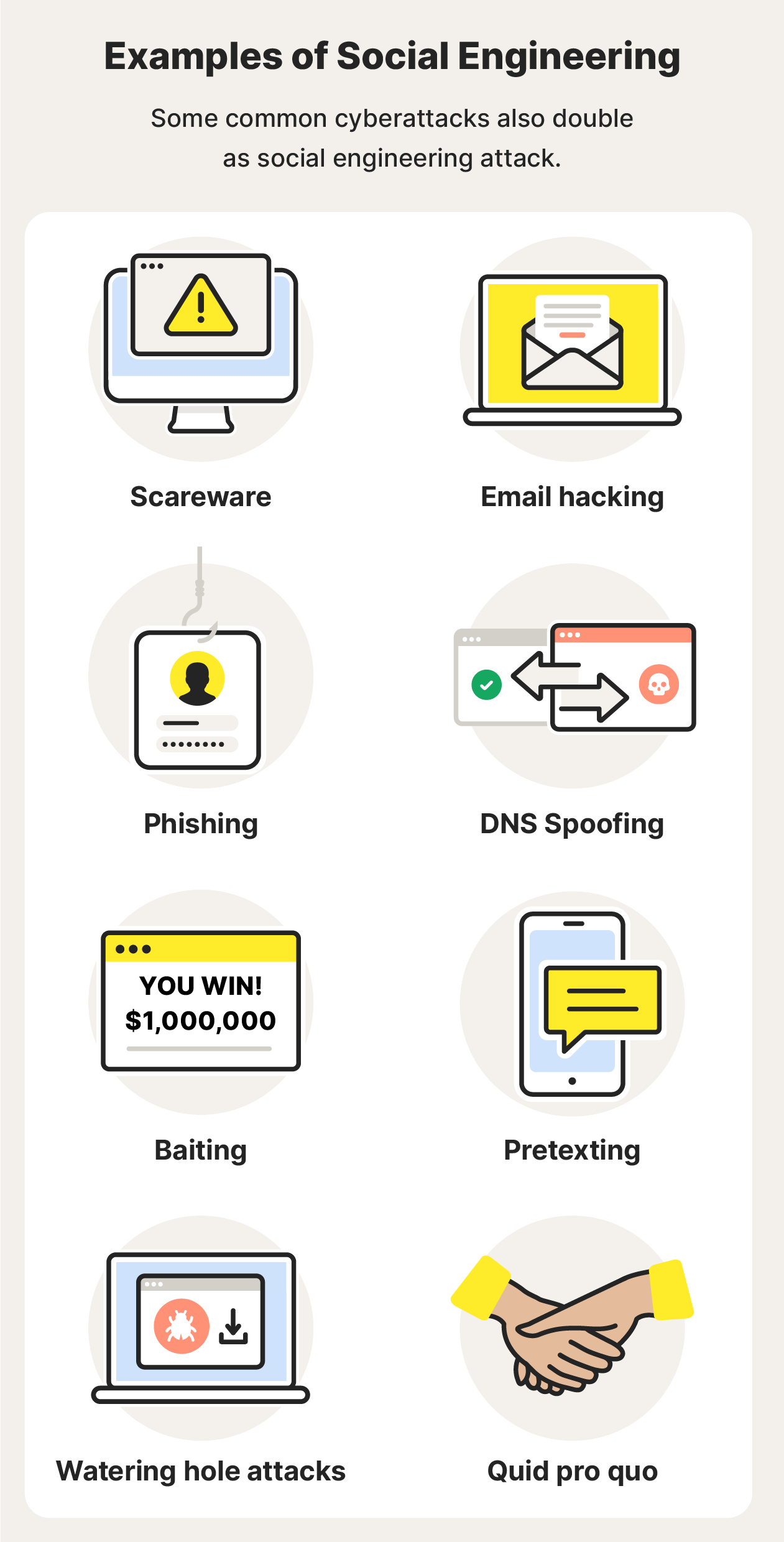
What is Social Engineering?

What is Social Engineering Attacks? ⚔️ Types, Examples.

Hackers Abusing OAuth Token to Take Over Millions of Accounts

Social engineering (security) - Wikipedia
Pawn Storm's Lack of Sophistication as a Strategy
What is social engineering? Definition + protection tips - Norton
DEF CON 29 - TIB AV-Portal
Recomendado para você
-
 How to Read Chess Moves In Algebraic Notation - The New York Times08 junho 2024
How to Read Chess Moves In Algebraic Notation - The New York Times08 junho 2024 -
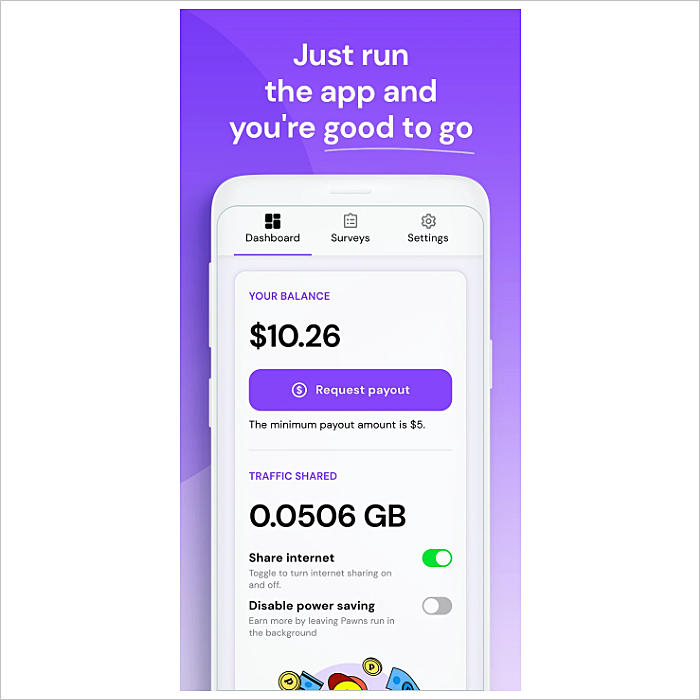 Pawns.app Review- Features, Pros, Cons, and MAD Rating08 junho 2024
Pawns.app Review- Features, Pros, Cons, and MAD Rating08 junho 2024 -
 Pawns.app on LinkedIn: 40 Cheap or Free Summer Activities That Don't Cost a Fortune - Pawns08 junho 2024
Pawns.app on LinkedIn: 40 Cheap or Free Summer Activities That Don't Cost a Fortune - Pawns08 junho 2024 -
 How to Stop Facebook From Making Us Pawns in Its Corporate Agenda08 junho 2024
How to Stop Facebook From Making Us Pawns in Its Corporate Agenda08 junho 2024 -
 ZOSI 2 Pack 1080P Home Security Cameras with Audio Recording,Built-in Microphone,1920TVL 2.0MP HD-TVI Surveillance Cameras with 120ft IR Night08 junho 2024
ZOSI 2 Pack 1080P Home Security Cameras with Audio Recording,Built-in Microphone,1920TVL 2.0MP HD-TVI Surveillance Cameras with 120ft IR Night08 junho 2024 -
Pawns.app on LinkedIn: Beyond Borders: Biggest Gaming Events Around the World - Pawns08 junho 2024
-
Pawns.app08 junho 2024
-
COMING TO THE SHOW? KNOW BEFORE YOU GO! Doors- 6 PM Pawn Shop Pearls on the Honky Tonk Stage - 8 PM @eliyoungband on the Main Stage -…08 junho 2024
-
 Share RPG battle maps with this open source web app08 junho 2024
Share RPG battle maps with this open source web app08 junho 2024 -
Hands-On Equations 1 - Microsoft Apps08 junho 2024
você pode gostar
-
 Download FIFA 16 MOD FIFA 23 Apk+Obb+Data Android Offline08 junho 2024
Download FIFA 16 MOD FIFA 23 Apk+Obb+Data Android Offline08 junho 2024 -
 BAUZINHO DA WEB - BAÚ DA WEB : Hamtaro desenhos e riscos para colorir, pintar, imprimir d…08 junho 2024
BAUZINHO DA WEB - BAÚ DA WEB : Hamtaro desenhos e riscos para colorir, pintar, imprimir d…08 junho 2024 -
CHESS NEWS BLOG: : The chess moods of chess great08 junho 2024
-
 Netflix and BBC Co-Production 'Champion' Season 1: Everything We Know So Far - What's on Netflix08 junho 2024
Netflix and BBC Co-Production 'Champion' Season 1: Everything We Know So Far - What's on Netflix08 junho 2024 -
 ArtStation - Ranni The Witch - Elden Ring Fanart08 junho 2024
ArtStation - Ranni The Witch - Elden Ring Fanart08 junho 2024 -
 Mirage QUEEN Prefers Circus08 junho 2024
Mirage QUEEN Prefers Circus08 junho 2024 -
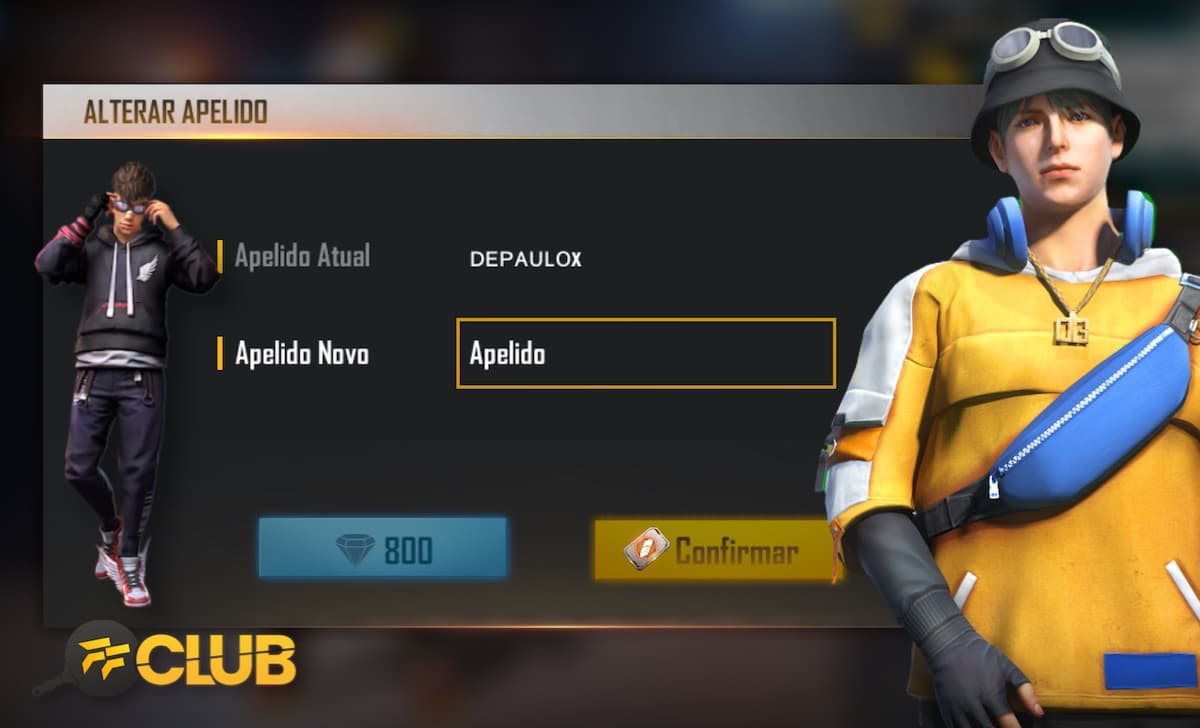 Nomes para Free Fire: masculino, instaplayer e mais nicks em abril08 junho 2024
Nomes para Free Fire: masculino, instaplayer e mais nicks em abril08 junho 2024 -
 Legend of Heroes Simulator codes08 junho 2024
Legend of Heroes Simulator codes08 junho 2024 -
 Souls Hero Tier List 2023: Best To Worst Heroes08 junho 2024
Souls Hero Tier List 2023: Best To Worst Heroes08 junho 2024 -
 Silhueta Perfil Uma Menina Solitária Triste Fundo Preto fotos, imagens de © NatalyLad #33077969408 junho 2024
Silhueta Perfil Uma Menina Solitária Triste Fundo Preto fotos, imagens de © NatalyLad #33077969408 junho 2024



